How Sniper Africa can Save You Time, Stress, and Money.
How Sniper Africa can Save You Time, Stress, and Money.
Blog Article
Sniper Africa Fundamentals Explained
Table of ContentsSniper Africa for DummiesGetting My Sniper Africa To WorkSniper Africa Can Be Fun For AnyoneSniper Africa Fundamentals ExplainedGetting My Sniper Africa To Work8 Easy Facts About Sniper Africa ExplainedLittle Known Questions About Sniper Africa.
This can be a certain system, a network location, or a theory activated by a revealed vulnerability or spot, information about a zero-day manipulate, an abnormality within the safety and security information set, or a request from elsewhere in the company. Once a trigger is recognized, the searching efforts are focused on proactively browsing for abnormalities that either prove or disprove the theory.
See This Report on Sniper Africa

This procedure may involve using automated tools and inquiries, along with hands-on analysis and relationship of data. Disorganized searching, also referred to as exploratory hunting, is an extra open-ended strategy to threat searching that does not depend on predefined requirements or theories. Instead, threat seekers utilize their expertise and intuition to look for potential dangers or vulnerabilities within a company's network or systems, commonly concentrating on locations that are viewed as high-risk or have a background of safety and security incidents.
In this situational technique, hazard seekers use risk knowledge, in addition to other pertinent information and contextual info concerning the entities on the network, to identify potential dangers or vulnerabilities related to the situation. This might entail the use of both structured and disorganized hunting methods, as well as cooperation with other stakeholders within the organization, such as IT, lawful, or service groups.
The Definitive Guide for Sniper Africa
(https://trello.com/w/sn1perafrica)You can input and search on threat intelligence such as IoCs, IP addresses, hash worths, and domain names. This process can be integrated with your safety information and occasion administration (SIEM) and threat intelligence devices, which make use of the intelligence to quest for risks. An additional terrific source of knowledge is the host or network artefacts provided by computer system emergency situation feedback groups (CERTs) or details sharing and analysis centers (ISAC), which might permit you to export computerized informs or share essential information regarding new strikes seen in various other companies.
The very first step is to determine proper teams and malware attacks by leveraging global discovery playbooks. This technique typically aligns with danger frameworks such as the MITRE ATT&CKTM structure. Here are the actions that are most frequently involved in the process: Usage IoAs and TTPs to identify risk stars. The seeker examines the domain name, environment, and strike habits to create a hypothesis that lines up with ATT&CK.
The goal is situating, identifying, and after that isolating the threat to avoid spread or spreading. The crossbreed danger hunting technique integrates all of the above methods, allowing security analysts to tailor the hunt.
What Does Sniper Africa Mean?
When operating in a safety procedures center (SOC), threat hunters report to the SOC manager. Some essential skills for an excellent threat seeker are: It is essential for danger hunters to be able to connect both vocally and in writing with wonderful quality concerning their activities, from examination completely through to findings and referrals for removal.
Information violations and cyberattacks cost organizations numerous bucks yearly. These tips can help your organization better discover these hazards: Threat seekers require to sift with strange activities and identify the actual threats, so it is critical to recognize what the normal operational tasks of the company are. To achieve this, the danger hunting group works together with essential personnel both within and outside of IT to collect useful info and insights.
The Greatest Guide To Sniper Africa
This process can be automated making use of an innovation like UEBA, which can show regular operation problems for an atmosphere, and the customers and machines within it. Danger hunters utilize this technique, borrowed from the armed forces, in cyber war.
Identify the correct program of action according to the occurrence condition. A danger searching group should have enough of the following: a danger hunting team that includes, at minimum, one experienced cyber risk seeker a fundamental risk hunting facilities that collects and organizes safety and security events and events software program made to recognize abnormalities and track down opponents Danger hunters use remedies and devices to locate dubious tasks.
Sniper Africa - Questions

Unlike automated risk discovery systems, hazard searching relies heavily on human intuition, matched by innovative devices. The stakes are high: A successful cyberattack can cause information violations, monetary losses, and reputational damage. Threat-hunting tools give security groups with the insights and capabilities needed to remain one action in advance of opponents.
Not known Facts About Sniper Africa
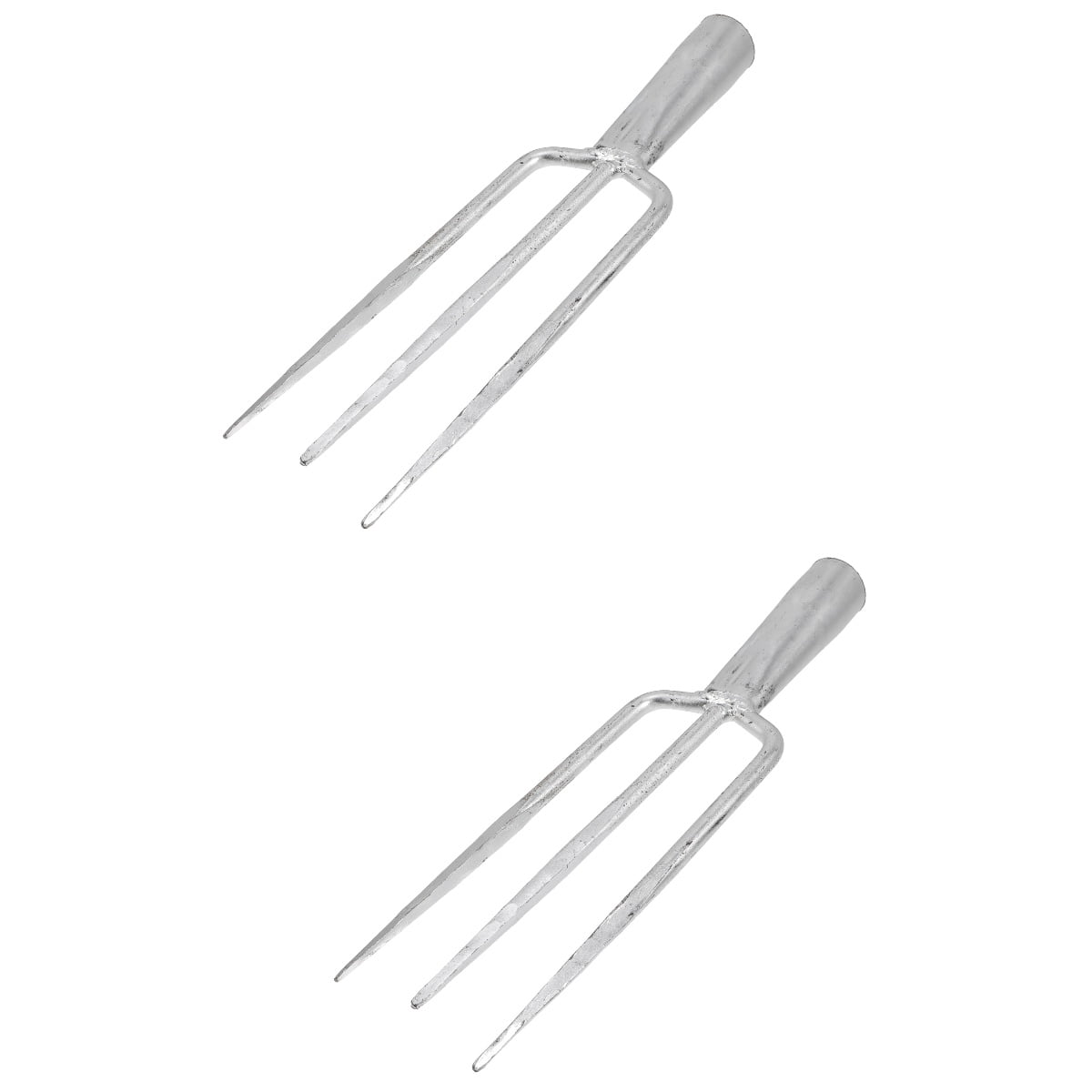
Here are the characteristics of reliable threat-hunting devices: Continuous surveillance of network website traffic, endpoints, and logs. Smooth compatibility with existing safety and security infrastructure. Hunting clothes.
Report this page